How To Block Phone Tracking

How to Block Phone Tracking: A Comprehensive Guide to Protecting Your Digital Privacy
Phone tracking is a pervasive threat to individual privacy, facilitated by a variety of technologies and actors. Understanding how phones are tracked and implementing robust blocking strategies is essential for anyone concerned about their digital footprint and personal security. This article delves into the multifaceted world of phone tracking and provides actionable methods to mitigate or eliminate it.
Understanding the Mechanisms of Phone Tracking
Before exploring how to block tracking, it’s crucial to comprehend the primary methods by which phones are tracked. These methods can be broadly categorized as:
1. Cellular Network Triangulation: This is one of the oldest and most fundamental tracking techniques. Mobile carriers maintain a network of cell towers. When your phone is active, it connects to the nearest tower. By measuring the signal strength and timing from multiple towers, your location can be pinpointed with a degree of accuracy. While this method is primarily used for network management and emergency services (like E911), it can be accessed by law enforcement with appropriate legal authorization and potentially by malicious actors through compromised network infrastructure or insider threats. The precision of triangulation varies, generally ranging from tens of meters in urban areas with dense tower coverage to kilometers in rural areas.
2. GPS (Global Positioning System): GPS is a satellite-based navigation system that allows devices to determine their precise location. Most smartphones have built-in GPS receivers. Apps, operating systems, and even web browsers can request and utilize GPS data for location-based services, navigation, and targeted advertising. The accuracy of GPS can be remarkably high, often within a few meters, especially with Assisted GPS (A-GPS), which uses cellular network data to speed up the initial fix. However, GPS relies on a clear line of sight to satellites, meaning it can be less effective indoors or in areas with significant signal obstruction.
3. Wi-Fi Positioning: Wi-Fi positioning systems leverage the known locations of Wi-Fi access points. Devices scan for nearby Wi-Fi networks and compare their MAC addresses and signal strengths against a database of Wi-Fi access points with known geographic coordinates. This method is particularly effective in urban environments where Wi-Fi density is high. Many apps and operating systems use Wi-Fi positioning as a primary or supplementary location service, especially when GPS signals are weak or unavailable. The accuracy can range from tens to hundreds of meters.
4. Bluetooth Beacons and Nearby Devices: Bluetooth technology, particularly Bluetooth Low Energy (BLE), is increasingly used for proximity detection. Small, low-power transmitters called beacons can be placed in various locations (e.g., retail stores, public transport) to broadcast a unique identifier. When your phone’s Bluetooth is enabled and an app has permission, it can detect these beacons and infer your presence in a specific area. Furthermore, the "Find My" networks (e.g., Apple’s Find My network) for both iPhones and Android devices allow for tracking of devices that are offline by utilizing the Bluetooth signals of other nearby user devices.
5. IP Address Geolocation: Every device connected to the internet is assigned an Internet Protocol (IP) address. While not as precise as GPS or cellular triangulation, IP addresses can be used to estimate a device’s general geographic location based on the IP address assigned by the Internet Service Provider (ISP). This data is often used for region-specific content delivery, targeted advertising, and basic location services by websites and applications. Accuracy can vary widely, from city-level to country-level.
6. IMEI and IMSI Tracking: The International Mobile Equipment Identity (IMEI) is a unique identifier for each mobile phone, while the International Mobile Subscriber Identity (IMSI) is a unique identifier for a SIM card. These identifiers can be used to track a device and its associated subscriber. Law enforcement and mobile carriers can track devices based on their IMEI and IMSI. Furthermore, "Stingrays" or IMSI catchers, sophisticated devices that mimic cell towers, can intercept and track all devices within their range by capturing their IMSI and IMEI.
7. App-Based Tracking: This is perhaps the most common and insidious form of tracking. Many applications, from social media platforms to seemingly innocuous utility apps, request and collect location data. This data is often used for targeted advertising, analytics, and to improve app services. Some apps are designed explicitly for tracking, such as parental control apps or employee monitoring software. This tracking can occur even when the app is not actively being used, if the app has been granted background location permissions.
8. Web Browser Tracking: Websites use various technologies like cookies, browser fingerprinting, and tracking pixels to monitor user activity, including browsing history, search queries, and even estimated location based on IP addresses. This information is often aggregated and used for personalized advertising and analytics.
Strategies for Blocking Phone Tracking
Implementing a layered approach to blocking phone tracking is the most effective strategy. This involves a combination of device settings, app management, and potentially external tools.
1. Master Your Device’s Location Services:
- Turn Off GPS and Location Services When Not Needed: This is the most fundamental step. On both iOS and Android, you can find a master switch for location services. Disable it entirely when you don’t require location-aware functionality.
- iOS: Go to Settings > Privacy & Security > Location Services. You can toggle Location Services off entirely, or manage permissions on a per-app basis.
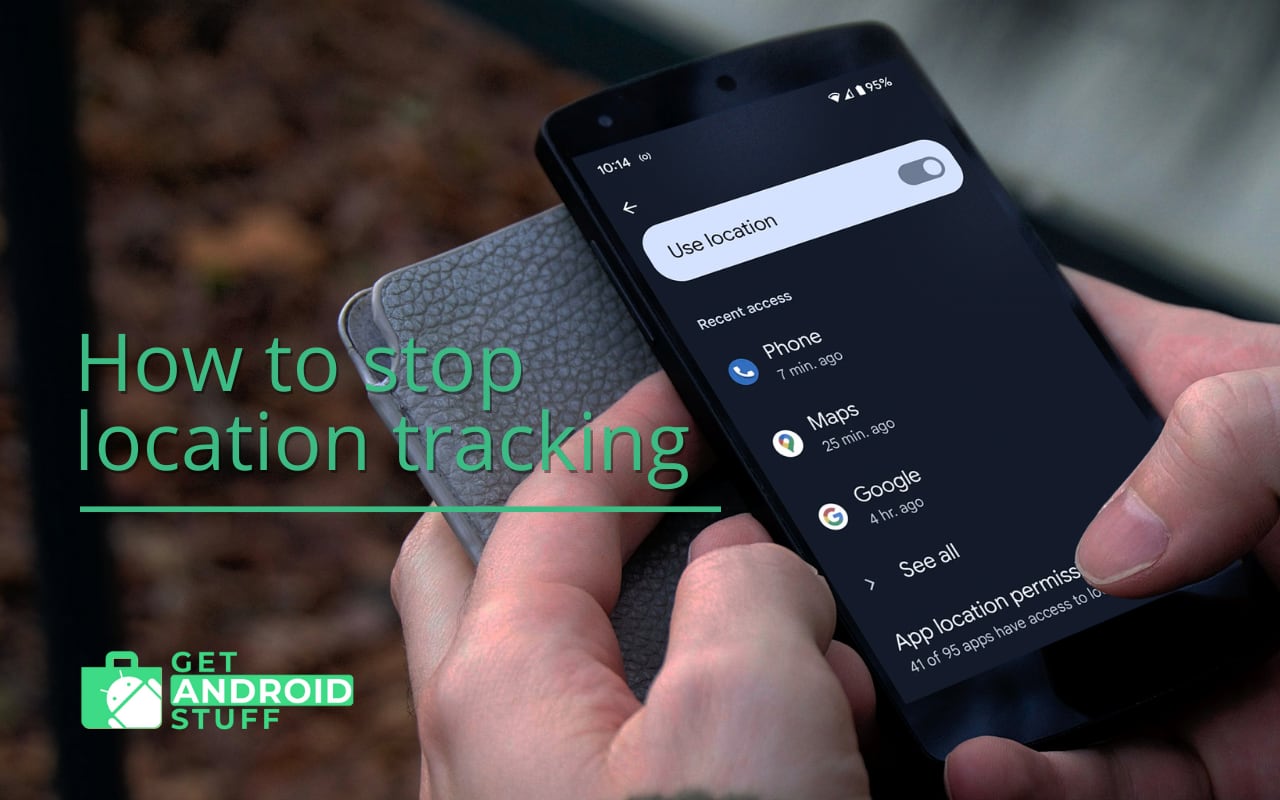
- Android: Go to Settings > Location. You can toggle Location off, or manage permissions for individual apps.
- Review App Permissions Regularly: Even if you’ve turned off master location services, individual apps can request location access. Make it a habit to review the location permissions for all installed apps. Grant access only to apps that genuinely need it for their core functionality, and consider setting some apps to "While Using the App" or "Ask Next Time" instead of "Always."
- iOS: Settings > Privacy & Security > Location Services. Scroll down to see each app and its permission level.
- Android: Settings > Location > App location permissions.
- Disable Wi-Fi and Bluetooth Scanning for Location: Both iOS and Android use Wi-Fi and Bluetooth scanning to improve location accuracy, even when Wi-Fi and Bluetooth are technically turned off for connectivity. This can still contribute to location tracking.
- iOS: Settings > Privacy & Security > Location Services > System Services. Here, you can disable Wi-Fi Networking, Bluetooth Networking, and Location-Based Alerts.
- Android: Settings > Location > Advanced (or similar). Look for options like "Wi-Fi scanning" and "Bluetooth scanning" and disable them.
2. Harden Your Apps:
- Uninstall Unnecessary Apps: The more apps you have installed, the greater the potential for data leakage. Regularly audit your installed apps and uninstall anything you don’t use or trust.
- Choose Privacy-Focused Alternatives: For common functionalities, opt for apps that prioritize privacy. For example, use privacy-respecting browsers, messaging apps with end-to-end encryption and minimal data collection, and search engines that don’t track your queries.
- Be Wary of Permissions During Installation: Pay close attention to the permissions an app requests during installation. If an app asks for broad access to your location, contacts, or other sensitive data that seems unnecessary for its stated purpose, it’s a red flag.
- Consider "Jailbreaking" (iOS) or "Rooting" (Android) with Extreme Caution: For advanced users, jailbreaking (iOS) or rooting (Android) can offer more granular control over system settings, including app permissions. However, this also carries significant security risks and can void warranties. It’s generally not recommended for most users.
3. Secure Your Network and Connectivity:
- Disable Wi-Fi and Bluetooth When Not in Use: While location services can still operate, turning off Wi-Fi and Bluetooth when you’re not actively using them reduces the opportunities for Bluetooth beacons and Wi-Fi positioning.
- Use a VPN (Virtual Private Network): A VPN encrypts your internet traffic and routes it through a server in a location of your choice. This masks your IP address, making it harder for websites and services to track your online activity and approximate your location. Choose a reputable VPN provider with a strong no-logs policy.
- Be Cautious of Public Wi-Fi: Public Wi-Fi networks are often unsecured and can be monitored by malicious actors. Avoid accessing sensitive information or performing financial transactions on public Wi-Fi. If you must use it, ensure you have a VPN enabled.
- Consider Turning Off Cellular Data When Not Needed: While this is less about tracking and more about reducing your digital footprint, disabling cellular data when you’re on Wi-Fi can limit some background data transfers that could potentially be used for tracking.
4. Mitigate Browser and Online Tracking:
- Use Privacy-Focused Browsers: Consider browsers like Brave, DuckDuckGo Privacy Browser, or Firefox with enhanced privacy settings. These browsers often block trackers by default and offer robust privacy features.
- Install Ad Blockers and Tracker Blockers: Browser extensions like uBlock Origin, Privacy Badger, and Ghostery can effectively block most ads and trackers, significantly reducing online surveillance.
- Clear Cookies and Cache Regularly: Regularly clearing your browser’s cookies and cache can help remove persistent tracking identifiers.
- Use Incognito/Private Browsing Modes: While not foolproof, incognito or private browsing modes prevent your browser from saving your browsing history, cookies, and site data.
- Disable JavaScript on Untrusted Websites: Many advanced tracking techniques rely on JavaScript. While this can break some website functionality, disabling JavaScript for untrusted sites can enhance privacy.
5. Advanced and Physical Security Measures:
- Use a Faraday Bag or Pouch: A Faraday bag is a shielded pouch that blocks all electromagnetic signals, including cellular, Wi-Fi, Bluetooth, and GPS. Placing your phone in a Faraday bag will effectively render it untrackable by radio frequency methods. These are often used by individuals requiring extreme privacy or security.
- Turn Off Your Phone Entirely: The most absolute way to prevent your phone from being tracked is to turn it off completely. When powered off, it cannot transmit or receive any signals.
- Be Mindful of SIM Cards: Your SIM card contains your IMSI, a unique identifier. While changing SIM cards doesn’t erase your phone’s history, it can complicate tracking if your phone is primarily being tracked via its SIM.
- Consider Burner Phones: For situations requiring absolute anonymity, using a temporary "burner" phone purchased with cash and used only for a specific purpose can be an option. However, these are still traceable if used carelessly.
- Understand "Find My" Networks: Be aware that even if your phone’s cellular and Wi-Fi are off, Apple’s Find My network and Google’s Find My Device network can still locate your device using the Bluetooth signals of other nearby devices. You can opt-out of these networks if you wish, but it means you won’t be able to locate your own lost device.
- iOS (Find My Network): Settings > [Your Name] > Find My > Find My iPhone > Find My network.
- Android (Find My Device network): Settings > Security > Find My Device. (Availability and exact path may vary by Android version and manufacturer).
6. Legal and Regulatory Considerations:
- Know Your Rights: In many jurisdictions, there are legal protections against unwarranted phone tracking. Understanding these laws can empower you to seek recourse if you believe your privacy has been violated.
- Be Aware of Terms of Service: When installing apps or using online services, take the time to review their terms of service and privacy policies. While often lengthy and complex, these documents outline how your data, including location data, will be used.
Conclusion:
Blocking phone tracking requires a proactive and informed approach. By understanding the various methods of tracking and diligently implementing the strategies outlined in this guide, individuals can significantly enhance their digital privacy and regain control over their personal information. The constant evolution of tracking technologies necessitates ongoing vigilance and a commitment to staying informed about the latest privacy best practices.