Httponly Secure Cookie Apache

The HttpOnly Flag: Enhancing Apache Cookie Security for Robust Web Applications
The HttpOnly flag for cookies is a critical security mechanism designed to mitigate the risk of cross-site scripting (XSS) attacks by preventing client-side scripts from accessing sensitive cookie values. When set, the HttpOnly attribute instructs the browser to disallow JavaScript from reading or manipulating cookies that possess this flag. This is particularly crucial for session cookies, authentication tokens, and any other cookie containing sensitive user information, as compromised client-side scripts can otherwise easily steal these values, leading to session hijacking, unauthorized access, and other severe security breaches. Apache, as a widely adopted web server, offers robust configuration options to leverage this security feature effectively.
Implementing the HttpOnly flag in Apache involves configuring the web server to append this attribute to cookies it sets. This is typically achieved through directives within Apache’s configuration files, primarily httpd.conf or within virtual host configurations. The most common and recommended method involves utilizing Apache’s Header directive, which allows for the modification or addition of HTTP headers sent in responses. By adding Set-Cookie headers with the HttpOnly attribute, administrators can ensure that all cookies served by Apache adhere to this security best practice. This proactive approach significantly hardens web applications against common XSS exploitation vectors, where attackers inject malicious scripts into web pages to steal cookies.
The core functionality of the HttpOnly flag lies in its browser-level enforcement. When a browser receives a Set-Cookie header containing HttpOnly, it flags that cookie internally. Subsequently, any JavaScript code attempting to access that cookie through properties like document.cookie will be denied permission. This effectively creates a barrier between potentially malicious client-side code and sensitive cookie data. For developers and system administrators, understanding this mechanism is paramount for building secure web applications. It’s not merely a configuration option but a fundamental security principle that should be applied universally to any cookie that doesn’t require direct JavaScript interaction.
Configuring Apache to set the HttpOnly flag can be done in several ways, offering flexibility based on the specific needs and complexity of the web application. The most straightforward approach is to use the Header directive within the main Apache configuration or a virtual host file. For instance, to enforce HttpOnly on all cookies, a directive like Header edit Set-Cookie "(.*)" "$1; HttpOnly" can be placed in the <VirtualHost> section or globally. This directive works by finding all Set-Cookie headers and appending ; HttpOnly to their existing values. It’s essential to understand that this is a blanket approach and might inadvertently affect cookies that do require JavaScript access, although such cases are generally rare for security-sensitive cookies.
A more granular control can be achieved by specifically targeting certain cookies. If an application sets a particular cookie, for example, sessionid, and it’s crucial to protect this cookie from JavaScript access, then the Header directive can be refined. However, directly targeting specific cookie names within the Header edit directive can become complex due to variations in cookie value formats. A more robust and common practice is to configure the application itself to set the HttpOnly flag when it generates the Set-Cookie header. This allows for precise control over which cookies receive the HttpOnly attribute based on their purpose and sensitivity. Many modern web frameworks have built-in support for setting the HttpOnly flag automatically for session cookies, simplifying this process significantly.
For scenarios where application-level control is not feasible or desired, Apache modules can provide alternative solutions. The mod_headers module, which is typically enabled by default in most Apache installations, is the primary tool for manipulating headers. The Header directive, as mentioned, is part of this module. If there’s a need for more complex header manipulation or conditional logic that the basic Header directive cannot handle, custom Apache modules could be developed, although this is a more advanced approach and usually unnecessary for simply adding the HttpOnly flag.
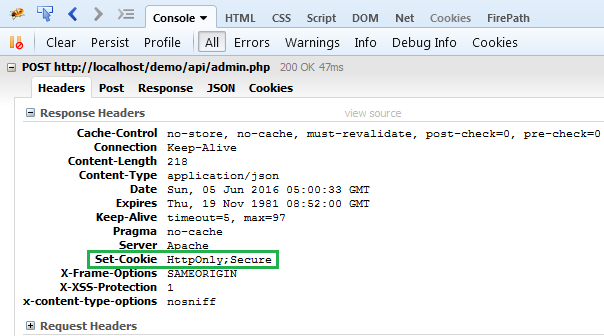
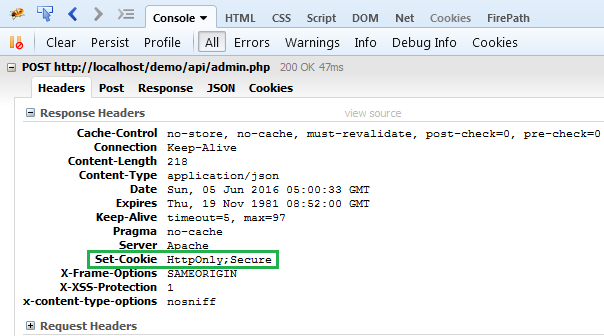
The Secure flag is another vital companion to the HttpOnly flag when securing cookies. While HttpOnly protects against XSS, the Secure flag ensures that the cookie is only transmitted over encrypted HTTPS connections. This prevents cookies from being intercepted in transit by attackers sniffing network traffic. It’s a fundamental recommendation to always use both HttpOnly and Secure flags for sensitive cookies, especially session identifiers. Apache can be configured to add the Secure flag similarly to the HttpOnly flag using the Header directive. For example, to enforce both flags on all cookies: Header edit Set-Cookie "(.*)" "$1; HttpOnly; Secure".
When implementing these security headers, it’s crucial to test thoroughly. Misconfigurations can lead to unexpected behavior. For instance, if a website relies on JavaScript to dynamically set or modify cookie values that should not be HttpOnly, enforcing it globally might break legitimate functionality. Therefore, a staged rollout or careful testing in development and staging environments is highly recommended before applying changes to a production Apache server. Browser developer tools are invaluable for verifying that cookies are being set with the intended flags. Inspecting the "Application" or "Storage" tab in Chrome’s developer tools, for example, will clearly indicate if the HttpOnly and Secure attributes are present for each cookie.
Beyond the basic implementation of HttpOnly, administrators should consider advanced security measures. Rate limiting and IP address tracking can help mitigate brute-force attacks against session cookies, even if they are protected by HttpOnly. Additionally, implementing strong session management practices, such as short session timeouts and the regeneration of session IDs upon login, further strengthens security. The HttpOnly flag is a powerful defense, but it’s most effective as part of a layered security strategy.
The importance of HttpOnly cannot be overstated in the current threat landscape. XSS vulnerabilities remain prevalent, and attackers are constantly refining their techniques to exploit them. By preventing JavaScript from accessing sensitive cookies, the HttpOnly flag directly neutralizes a primary avenue for session hijacking. This is especially relevant for web applications handling user accounts, financial transactions, or any data that, if compromised, could lead to significant harm. The simplicity of its implementation, coupled with its profound security benefits, makes it an essential configuration for any Apache-powered web server.
For developers working with Apache, understanding how their chosen web framework interacts with cookie settings is key. Most modern frameworks abstract away much of the low-level HTTP header manipulation. However, it’s still important to be aware of the underlying mechanisms and to ensure that the framework’s default settings are secure. If a framework doesn’t automatically set HttpOnly for session cookies, it’s a strong indicator that manual configuration on the Apache server or within the application’s code is necessary.
The decision to enforce HttpOnly globally versus on a per-cookie basis depends on the application’s architecture and security requirements. For highly sensitive applications where JavaScript access to cookies is never intended, a global enforcement via Apache’s Header directive can be a straightforward and effective solution. However, for more complex applications with diverse cookie usage, a more nuanced approach, often managed at the application level, might be preferred. In such cases, developers should explicitly configure their applications to add the HttpOnly flag to all security-sensitive cookies.
In conclusion, the HttpOnly flag is a cornerstone of modern web security, and its effective implementation on Apache servers is paramount for protecting web applications from XSS attacks. By leveraging Apache’s Header directive and, where appropriate, configuring applications to set this flag, administrators and developers can significantly enhance the security posture of their websites. Combined with the Secure flag and other robust security practices, HttpOnly provides a critical layer of defense against prevalent threats, ensuring the integrity and confidentiality of user data. Continuous vigilance, thorough testing, and adherence to security best practices are essential for maintaining a secure online environment.




