Find Python Security Vulnerabilities

Uncovering Python Security Vulnerabilities: A Comprehensive Guide for Developers and Security Professionals
Python’s widespread adoption across web development, data science, and automation has made it a cornerstone of modern software engineering. However, this popularity also makes it a prime target for attackers. Understanding and mitigating Python security vulnerabilities is paramount for protecting applications and sensitive data. This guide provides an in-depth look at common Python security flaws, their detection methods, and remediation strategies, aiming to equip developers and security professionals with the knowledge to build more secure Python applications.
SQL Injection represents a significant threat in applications that interact with databases. In Python, this vulnerability arises when user-supplied input is directly incorporated into SQL queries without proper sanitization or parameterization. An attacker can craft malicious input strings that, when executed by the database, manipulate the intended query. For instance, if a web application uses a query like SELECT * FROM users WHERE username = ' + user_input + ', an attacker could provide ' OR '1'='1 as input, effectively bypassing authentication by returning all user records. Detecting SQL injection often involves code reviews, static analysis tools, and dynamic analysis through penetration testing. The primary defense against SQL injection in Python is to never directly concatenate user input into SQL queries. Instead, developers must utilize parameterized queries or prepared statements provided by database connectors (e.g., psycopg2 for PostgreSQL, mysql.connector for MySQL). These methods ensure that user input is treated as data, not executable SQL code, effectively neutralizing the threat. Object-Relational Mappers (ORMs) like SQLAlchemy and Django’s ORM also offer built-in protection against SQL injection when used correctly, as they abstract away direct SQL construction.
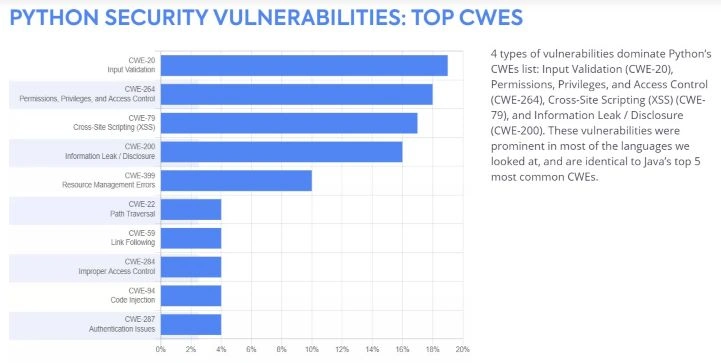
Cross-Site Scripting (XSS) attacks exploit vulnerabilities in web applications to inject malicious scripts into web pages viewed by other users. In Python web frameworks like Flask or Django, XSS can occur when user-provided data is displayed on a webpage without proper escaping. If an application renders user input directly, an attacker could inject HTML and JavaScript code, such as <script>alert('XSS')</script>. This script would then execute in the victim’s browser, potentially stealing session cookies, redirecting users to malicious sites, or performing actions on behalf of the user. Identifying XSS vulnerabilities typically involves manual code inspection, browser developer tools to observe how data is rendered, and automated security scanners. The most effective defense against XSS in Python is output encoding. This means transforming potentially harmful characters (like <, >, &, ", ') into their HTML entity equivalents before rendering them. Most Python web frameworks provide templating engines (e.g., Jinja2 for Flask, Django’s built-in templating system) that automatically escape variables by default. Developers must ensure that this auto-escaping feature is enabled and not overridden, and if they are manually constructing HTML, they must use functions like html.escape() from Python’s built-in html module.
Insecure Deserialization is a critical vulnerability that arises when untrusted data is deserialized (converted from a byte stream back into a Python object) without proper validation. Python’s pickle module, for instance, is notoriously susceptible to this. If an attacker can control the data being pickled and unpickled, they can craft malicious payloads that, when deserialized, execute arbitrary code on the server. A common attack vector involves sending a specially crafted pickle stream that, upon unpickling, calls a system command. For example, deserializing data containing __reduce__ or __reduce_ex__ methods can lead to code execution. Detecting insecure deserialization often requires reviewing code that handles serialized data, especially from external sources. Static analysis tools can flag the use of pickle with untrusted input. The most robust solution is to avoid deserializing untrusted data altogether, especially with pickle. If deserialization is unavoidable, consider using safer formats like JSON or YAML and ensure that any custom deserialization logic rigorously validates the structure and content of the data before any potentially dangerous operations are performed. For Python objects, consider safer serialization libraries like json (which only supports basic data types) or msgpack with strict validation.
Authentication bypass vulnerabilities allow unauthorized users to gain access to protected resources. In Python applications, this can manifest in several ways, including weak password policies, improper session management, or insecure implementation of authentication mechanisms. For instance, a poorly designed login system might allow users to bypass authentication by manipulating request parameters or by exploiting flaws in the password reset mechanism. Detecting these vulnerabilities requires thorough testing of the authentication flow, including attempts to guess passwords, tamper with session tokens, and exploit known bypass techniques. Remediation involves implementing strong authentication practices: enforcing complex password policies, securely storing password hashes (using libraries like bcrypt or argon2), implementing multi-factor authentication (MFA), and employing secure session management techniques (e.g., using secure, HTTP-only cookies with appropriate expiration times). Rate limiting login attempts and implementing account lockout mechanisms are also crucial.
Authorization flaws, also known as Access Control issues, occur when an application incorrectly restricts access to resources. Even if a user is authenticated, they might be able to access data or perform actions they are not permitted to. In Python applications, this often involves flaws in how roles and permissions are checked. For example, an application might rely solely on client-side checks, which are easily circumvented, instead of robust server-side validation. Detecting these vulnerabilities requires testing different user roles to ensure that they can only access what they are supposed to. Static analysis can help identify missing or weak authorization checks. The solution lies in implementing principle of least privilege and robust server-side authorization checks. Every request that accesses a protected resource or performs a sensitive action must be validated against the authenticated user’s permissions. Frameworks like Flask and Django offer mechanisms for role-based access control (RBAC) that should be leveraged.
Cross-Site Request Forgery (CSRF) attacks trick authenticated users into performing unintended actions on a web application they are logged into. In Python web applications, this can happen if sensitive actions (like changing an email address or making a purchase) do not have CSRF protection. An attacker crafts a malicious link or form that, when clicked by an authenticated user, submits a request to the vulnerable application, performing the unwanted action on behalf of the user. Identifying CSRF vulnerabilities involves checking sensitive endpoints for the absence of CSRF tokens. The standard defense against CSRF in Python web frameworks is the use of synchronizer tokens. These are unique, unpredictable tokens generated by the server for each user session. The server embeds these tokens in forms or hidden fields. When the client submits a form, the token is sent back. The server then validates that the token matches the one associated with the user’s session. If they don’t match, the request is rejected. Major Python web frameworks like Django and Flask provide built-in CSRF protection middleware that should be enabled and properly configured.
File Upload Vulnerabilities can arise when applications allow users to upload files without proper validation of file types, sizes, or content. Attackers can exploit this by uploading malicious files, such as executable scripts or web shells, which can then be executed on the server, leading to code execution or denial-of-service. Detecting these vulnerabilities involves attempting to upload various file types, including executables, scripts, and files with malicious content. The primary mitigation strategy is rigorous file validation. This includes: validating file extensions against an allowlist of permitted types, checking file MIME types, enforcing strict file size limits, and performing content-based scanning (e.g., using antivirus or specialized parsers) to detect malicious content. Storing uploaded files outside the webroot and with non-executable permissions is also crucial.
Command Injection vulnerabilities occur when user input is used to construct system commands that are then executed by the operating system. In Python, this is often seen when functions like os.system(), subprocess.call(), or subprocess.run() are used with unsanitized user input. An attacker can inject special characters (like ;, |, &) to append arbitrary commands to the intended ones, leading to arbitrary code execution. For example, if a script executes os.system("ping " + user_input), an attacker could provide example.com; rm -rf /. Detecting command injection involves reviewing code that utilizes these functions and looking for direct concatenation of user input into command strings. The best practice is to avoid executing external commands with user-supplied input whenever possible. If it is absolutely necessary, use the subprocess module with its shell=False argument and pass commands and arguments as a list, ensuring that each argument is treated as a distinct, safe piece of data. For commands that must be executed with shell=True, extensive sanitization and validation of the input are critical, though this approach is generally discouraged.
XML External Entity (XXE) vulnerabilities affect applications that parse XML input. If an application parses XML from an untrusted source without disabling external entity processing, an attacker can craft XML documents that reference external entities. These entities can be used to access sensitive files on the server, perform denial-of-service attacks, or conduct server-side request forgery (SSRF). In Python, libraries like xml.etree.ElementTree or lxml can be vulnerable if not configured correctly. Detecting XXE involves inspecting XML parsing code and testing with crafted XML payloads that include external entity declarations. The crucial mitigation step is to disable the processing of external entities when parsing XML from untrusted sources. For the standard xml.etree.ElementTree library, this is achieved by using XMLParser(resolve_entities=False). For lxml, it involves setting the resolve_entities parameter to False during parsing.
Server-Side Request Forgery (SSRF) vulnerabilities allow an attacker to induce the server-side application to make HTTP requests to an arbitrary domain of the attacker’s choosing. This can be used to scan internal networks, access internal services that are not directly exposed to the internet, or interact with cloud provider metadata services to steal credentials. In Python, SSRF often arises when applications fetch resources based on user-provided URLs without proper validation. Detecting SSRF involves attempting to make requests to internal IP addresses, localhost, or cloud metadata endpoints. The primary defense is strict URL validation and whitelisting. Only allow requests to explicitly permitted domains or IP addresses. Sanitize and validate all user-provided URLs, and reject any that do not conform to expected patterns.
Using outdated or vulnerable dependencies is a significant security risk. Python’s rich ecosystem of third-party libraries means that applications often rely on many external packages. If these packages have known vulnerabilities, the application inherits those risks. This is often referred to as the "supply chain attack" vector. Detecting these vulnerabilities is a continuous process. Tools like safety or dependabot can scan your project’s dependencies for known CVEs (Common Vulnerabilities and Exposures). Regularly updating dependencies to their latest secure versions is the most effective remediation strategy. Integrating automated dependency scanning into your CI/CD pipeline ensures that new vulnerabilities are detected promptly. When a vulnerability is found in a dependency, investigate if a patch is available. If not, consider migrating to an alternative library or implementing compensating controls to mitigate the risk.
Logging and Monitoring are not direct vulnerability types but are critical for detecting and responding to security incidents. Insufficient or insecure logging can leave an application blind to ongoing attacks. For example, if login attempts, access control failures, or errors are not logged, it becomes difficult to identify a brute-force attack or an unauthorized access attempt. Secure logging involves logging relevant security events, ensuring logs are stored securely, and implementing monitoring and alerting mechanisms to detect suspicious patterns. Centralized logging solutions and Security Information and Event Management (SIEM) systems can aggregate and analyze logs from multiple sources, providing valuable insights into potential security breaches.
In conclusion, building secure Python applications requires a proactive and multi-layered approach to security. By understanding common vulnerabilities like SQL Injection, XSS, insecure deserialization, authentication and authorization flaws, CSRF, file upload issues, command injection, XXE, SSRF, and dependency management, developers can implement robust defenses. This involves employing secure coding practices, utilizing framework-provided security features, performing regular code reviews and security testing, and staying vigilant about dependency updates. A commitment to continuous security improvement is essential in the ever-evolving threat landscape.