What Is Phishing Attack
Phishing Attacks: A Comprehensive Guide to Understanding and Mitigating This Cyber Threat
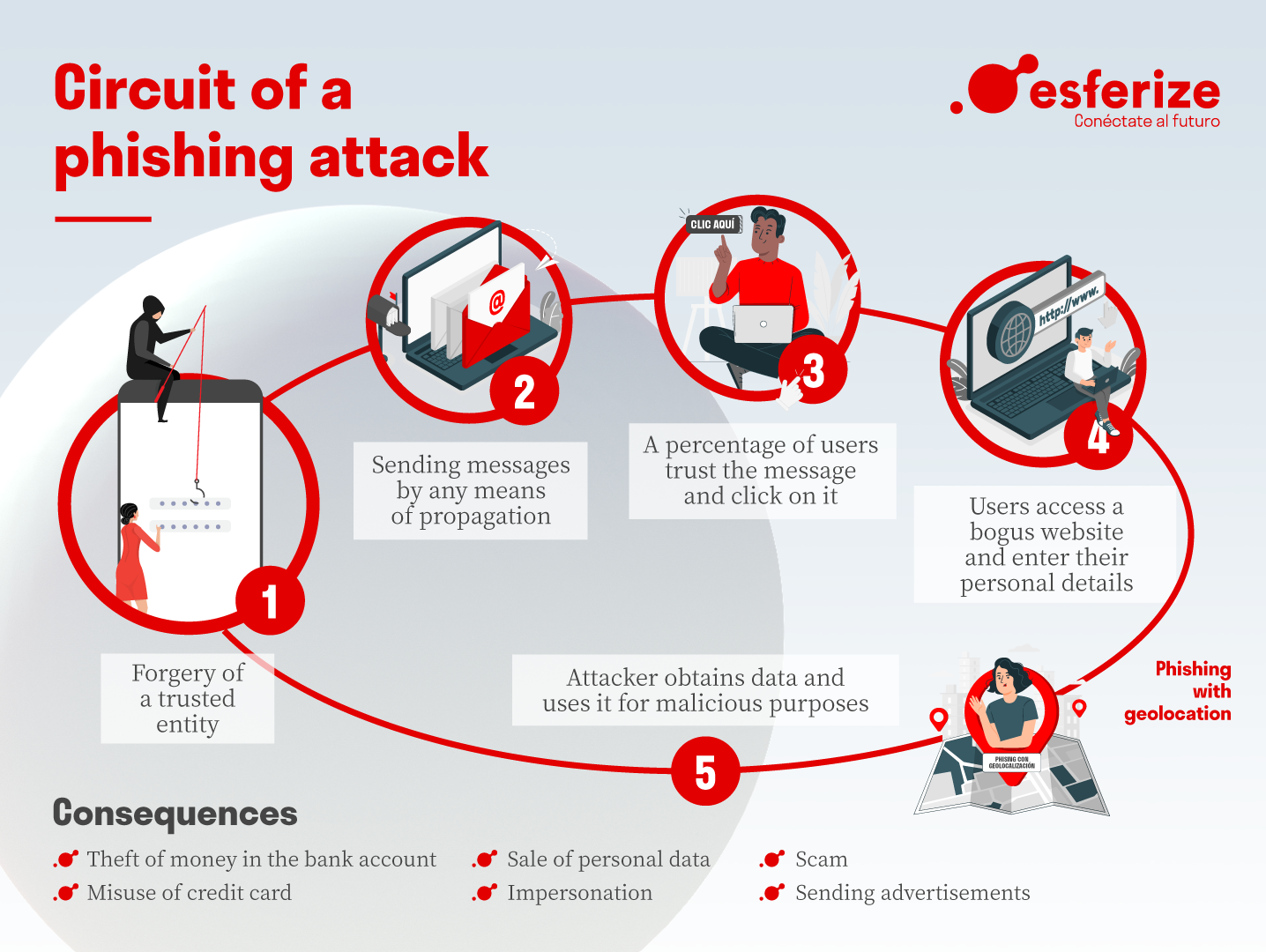
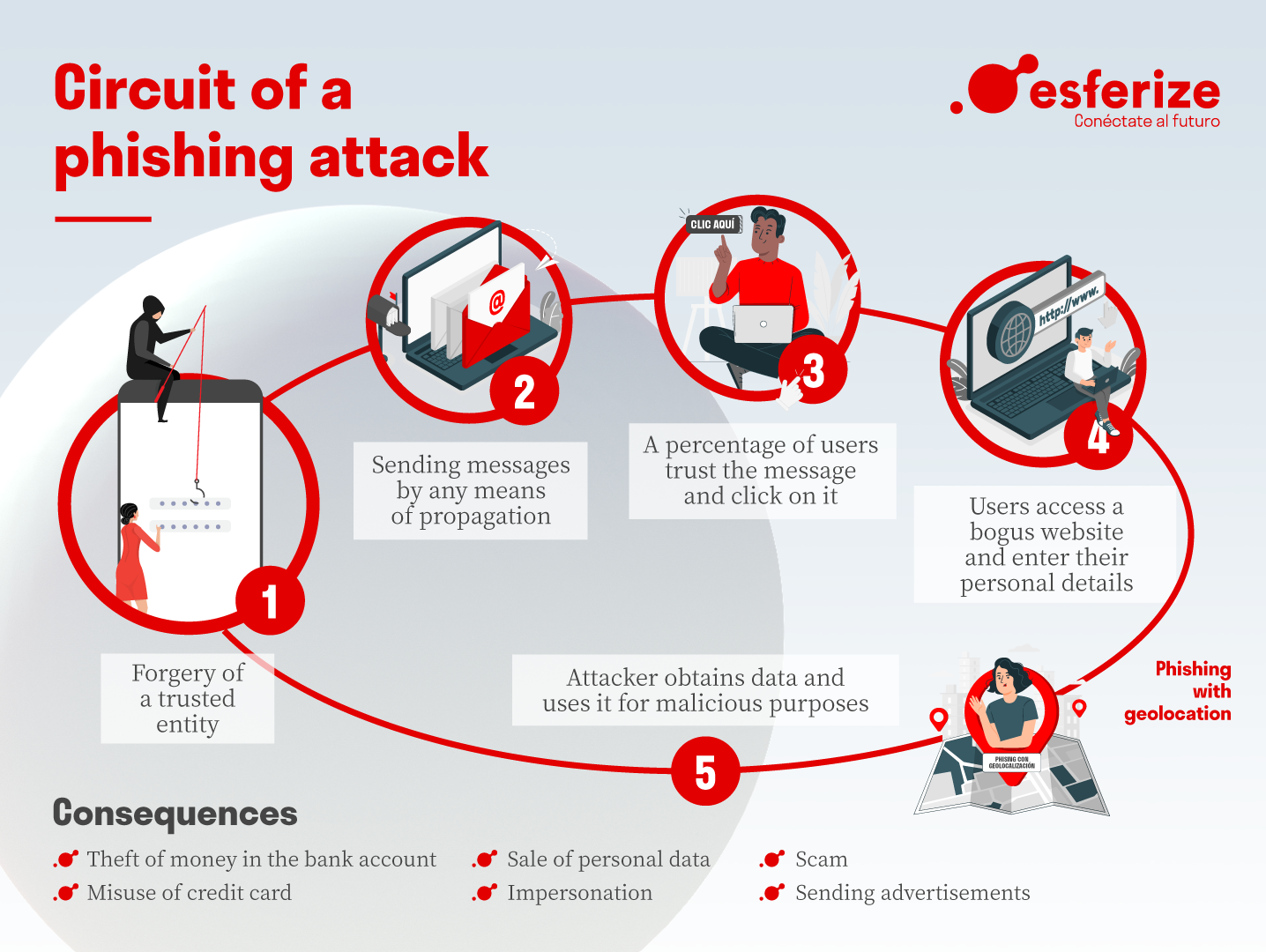
Phishing attacks are a prevalent and constantly evolving form of cybercrime that targets individuals and organizations by masquerading as legitimate entities. The primary objective of a phishing attack is to trick unsuspecting victims into divulging sensitive information such as usernames, passwords, credit card details, social security numbers, or other personal identifying information (PII). This stolen data is then used for financial gain, identity theft, or to facilitate further malicious activities like ransomware deployment or corporate espionage. Phishing attacks exploit human psychology, leveraging trust, urgency, fear, or curiosity to manipulate recipients into taking actions that compromise their security. The digital landscape, with its reliance on email, messaging apps, and social media, provides fertile ground for these deceptive campaigns. Understanding the mechanics, motivations, and diverse forms of phishing is crucial for effective defense.
The fundamental modus operandi of a phishing attack involves deception. Attackers craft communications that appear to originate from trusted sources. These sources can range from well-known companies like banks, e-commerce platforms (e.g., Amazon, eBay), social media networks (e.g., Facebook, LinkedIn), government agencies (e.g., IRS, tax authorities), or even internal IT departments. The impersonation is often highly sophisticated, mimicking the branding, logos, tone, and even the email addresses of the legitimate entities. The communication, typically an email but increasingly occurring via text messages (smishing) or voice calls (vishing), presents a scenario designed to elicit an immediate response. Common lures include notifications of suspicious account activity, urgent security alerts, prize winnings, account verification requests, or even fake invoices requiring immediate payment. The goal is to bypass rational thought and trigger an impulsive action.
Once the victim is sufficiently enticed or alarmed, the phishing attack directs them towards a malicious payload. This payload can manifest in several ways. The most common is a hyperlink embedded within the deceptive message. Clicking this link will redirect the user to a fraudulent website that closely resembles the legitimate site they intended to visit. This fake website will then prompt the user to enter their login credentials or other sensitive data. Alternatively, the malicious communication might contain an attachment. This attachment, often disguised as a document (e.g., PDF, Word document) or an executable file, can harbor malware, such as viruses, spyware, or ransomware, which, upon opening, infects the user’s device and can lead to data exfiltration or system compromise.
The motivations behind phishing attacks are primarily financial and strategic. For individual cybercriminals, the stolen credentials can be sold on the dark web, used to access bank accounts, or to make fraudulent purchases. Larger, more organized criminal enterprises may use phishing to steal identities for widespread fraud or to gain access to corporate networks, paving the way for more significant financial exploits like ransomware attacks that cripple businesses. Nation-state actors may employ phishing to gather intelligence, disrupt critical infrastructure, or influence political outcomes by targeting government officials, journalists, or activists. The low cost of execution and the high potential for reward make phishing an attractive criminal enterprise.
The landscape of phishing attacks is not monolithic; rather, it encompasses a variety of specialized techniques, each with its own characteristics and target audience. Spear Phishing is a highly targeted form of phishing where attackers conduct extensive research on their intended victims. This research allows them to personalize the phishing message, making it far more convincing. For example, a spear-phishing email might reference a specific project the victim is working on, a colleague’s name, or a recent event within their organization, increasing the likelihood of engagement. The intelligence gathered for spear phishing can come from publicly available sources like LinkedIn profiles, company websites, or social media, or through prior reconnaissance.
A more advanced and dangerous variant is Whaling, also known as CEO fraud or business executive phishing. Whaling specifically targets high-profile individuals within an organization, such as CEOs, CFOs, or other senior executives. The goal is often to trick these individuals into authorizing large financial transfers or divulging highly sensitive corporate information. The messages in whaling attacks are crafted with extreme precision, often impersonating other executives or trusted external advisors. The potential financial and reputational damage from a successful whaling attack can be catastrophic for a business.
Clone Phishing involves taking a legitimate email that a user has already received, copying its content, and then sending a modified version with malicious links or attachments. This is particularly effective because the recipient recognizes the sender and the general content, making it less suspicious. For instance, a clone phishing attack might take a legitimate bank statement notification and alter the link to point to a fake login page.
Business Email Compromise (BEC) is a broad category that encompasses several types of phishing attacks targeting businesses. While often overlapping with whaling and spear phishing, BEC attacks specifically focus on financial fraud by impersonating trusted business partners, vendors, or even internal executives. The most common BEC tactic involves an attacker impersonating a vendor and sending an invoice or a request for a change in payment details. The employee responsible for processing payments, if not vigilant, can then be tricked into wiring funds to the attacker’s account.
Smishing (SMS Phishing) and Vishing (Voice Phishing) represent phishing attacks that have expanded beyond email to other communication channels. Smishing attacks use text messages to lure victims into clicking malicious links or calling fraudulent phone numbers. These messages often mimic those from shipping companies, banks, or government agencies, creating a sense of urgency. Vishing attacks involve phone calls where scammers impersonate legitimate organizations to extract information or solicit money. They might claim to be from the IRS, a tech support company, or even a law enforcement agency, using social engineering tactics to pressure victims.
Defending against phishing attacks requires a multi-layered approach, encompassing both technological solutions and robust user education. On the technological front, organizations employ several key defenses. Email Security Filters are designed to detect and block malicious emails before they reach user inboxes. These filters utilize various techniques, including spam detection, URL analysis, attachment scanning for malware, and reputation-based blocking of known malicious IP addresses and domains. Web Filters can prevent users from accessing known phishing websites by blocking access to malicious URLs. Multi-Factor Authentication (MFA) is a critical defense that adds an extra layer of security beyond just a password. Even if an attacker obtains a user’s credentials through phishing, they would still need a second form of authentication (e.g., a code from a mobile app or a hardware token) to gain access, significantly reducing the risk of account compromise.
However, technology alone is insufficient. User Education and Awareness Training are paramount. Employees need to be trained to recognize the common red flags of phishing attacks. This includes scrutinizing sender email addresses for subtle misspellings or unusual domains, being wary of unsolicited emails requesting sensitive information, hovering over links to preview their destination URL without clicking, and exercising caution with unexpected attachments. Regular training sessions, simulated phishing exercises, and clear reporting procedures for suspicious emails empower users to become the first line of defense.
Security Policies and Procedures are also vital. Organizations should have clear guidelines on handling sensitive information, verifying payment requests, and reporting security incidents. Implementing a "least privilege" principle, where users are granted only the necessary access to perform their job functions, can also limit the damage an attacker can inflict if they successfully compromise an account.
The evolving nature of phishing attacks necessitates continuous adaptation and vigilance. As attackers refine their techniques, so too must defenses. The rise of AI-powered phishing attacks, capable of generating highly personalized and sophisticated lures at scale, presents a new frontier of challenges. These advanced threats require more intelligent and adaptive security solutions, alongside an even greater emphasis on human awareness and critical thinking. The persistent threat of phishing underscores the ongoing need for a proactive and comprehensive cybersecurity strategy that integrates technology, education, and robust processes to safeguard individuals and organizations in the digital realm.