Best Non Custodial Wallets
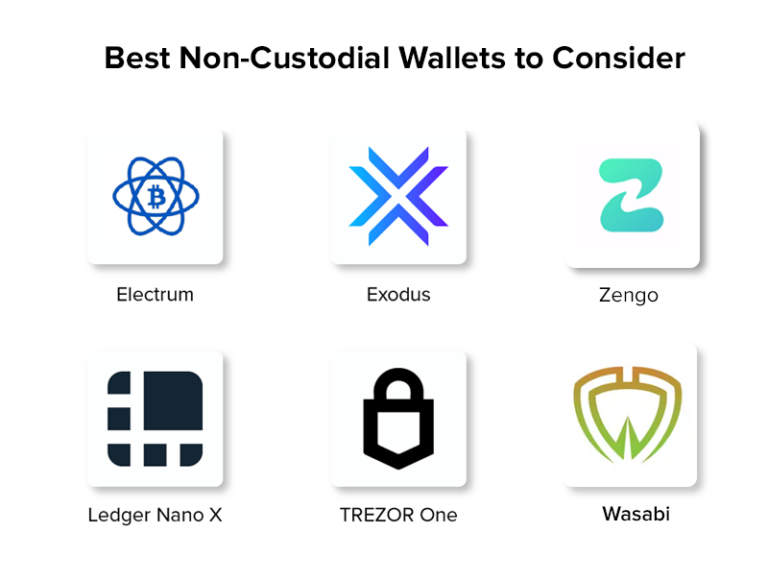
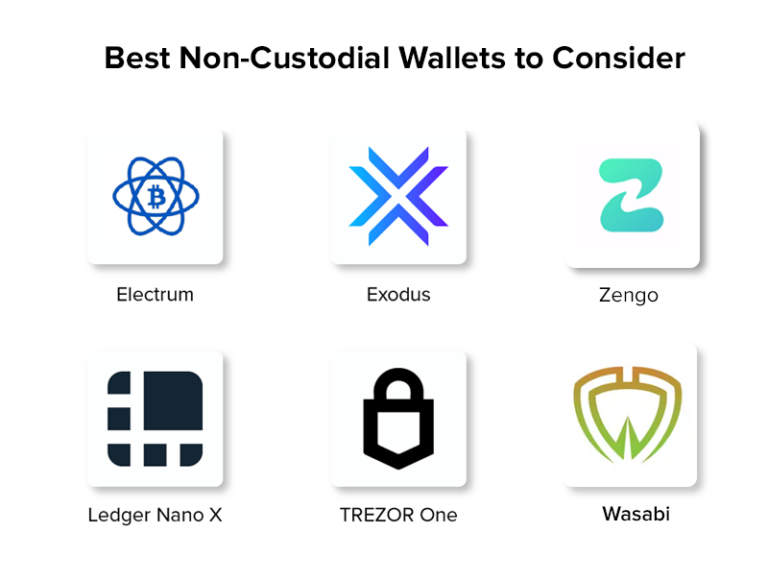
The Apex of Digital Asset Control: A Definitive Guide to the Best Non-Custodial Wallets
Choosing the right non-custodial wallet is paramount for any individual serious about securely managing their digital assets. Unlike custodial solutions where a third party holds your private keys, non-custodial wallets empower you with complete ownership and control. This means you are the sole guardian of your cryptographic treasures, responsible for their safekeeping and recovery. The advantages are significant: enhanced security against exchange hacks, greater privacy as you don’t rely on a central authority, and the ability to interact with the decentralized web (dApp) ecosystem without intermediaries. However, this freedom comes with the responsibility of safeguarding your private keys or seed phrase. Losing them unequivocally means losing access to your funds, permanently. The following delves into the leading non-custodial wallet options, analyzing their features, security protocols, supported assets, and user experience to aid in making an informed decision.
Understanding the Core Tenets of Non-Custodial Security
At the heart of non-custodial wallet security lies the concept of private key management. Your private key is the secret code that grants you access to and control over your cryptocurrency holdings on the blockchain. It’s essentially your digital signature. When you send crypto, your private key is used to sign the transaction, proving ownership. Non-custodial wallets generate and store these keys locally on your device or a dedicated hardware device, never transmitting them to a third-party server. This decentralization of key management is the fundamental differentiator from custodial wallets.
The second crucial element is the seed phrase, also known as a recovery phrase or mnemonic phrase. This is a sequence of 12, 18, or 24 random words that can be used to regenerate your private keys. It acts as a master key. If you lose access to your wallet device, you can use your seed phrase to restore your funds on a new device or a different compatible wallet. The security of your non-custodial wallet hinges entirely on the secure storage of both your private keys (which are usually derived from your seed phrase) and especially your seed phrase itself. Physical storage, often offline, is strongly recommended, eschewing digital backups that could be vulnerable to malware or hacking.
Hardware Wallets: The Gold Standard for Cold Storage
For individuals holding significant amounts of cryptocurrency or those prioritizing the highest level of security, hardware wallets are the undisputed champions. These are physical devices, resembling USB drives, specifically designed to store your private keys offline, even when connected to an internet-enabled computer. This "cold storage" approach isolates your private keys from online threats, making them exceptionally resilient to malware, phishing attacks, and remote hacking attempts.
Ledger Nano S Plus/X: Ledger has established itself as a market leader with its Nano S Plus and Nano X models. Both offer robust security, employing a Secure Element chip, akin to those used in credit cards and passports, to safeguard your private keys. The Nano S Plus is a more budget-friendly option, while the Nano X boasts Bluetooth connectivity for seamless mobile integration, albeit with a slightly higher price point. They support a vast array of cryptocurrencies and tokens, managed through the Ledger Live desktop and mobile application. The user interface is generally intuitive, and the devices guide you through setup, transaction signing, and backup processes with on-screen prompts. Security updates are regularly provided through Ledger Live, ensuring ongoing protection against emerging vulnerabilities.
Trezor Model T/One: Trezor, another pioneer in the hardware wallet space, offers the Model T and the more affordable Model One. The Model T features a touchscreen interface for enhanced usability and PIN entry, while the Model One relies on physical buttons. Both utilize an open-source firmware approach, which some users find more transparent and trustworthy. Trezor wallets are known for their user-friendly interface and extensive coin support. Similar to Ledger, they require a seed phrase backup and offer secure offline storage of private keys. The Trezor Suite desktop application manages your assets and facilitates firmware updates.
Key Advantages of Hardware Wallets:
- Unparalleled Security: Private keys stored offline, immune to online threats.
- Tamper-Proof: Secure element chips and physical security measures.
- Ease of Use (Relatively): Dedicated interfaces guide users through secure operations.
- Broad Asset Support: Typically support hundreds of different cryptocurrencies and tokens.
- Ideal for Long-Term Holding (HODLing): Minimizes risk for significant investments.
Disadvantages of Hardware Wallets:
- Cost: Generally more expensive than software wallets.
- Physical Vulnerability: Can be lost, stolen, or damaged, necessitating a robust seed phrase backup.
- Slightly Less Convenient for Frequent Trading: Transactions require physical interaction with the device.
Software Wallets: Balancing Accessibility and Control
Software wallets, also known as hot wallets, are applications that run on your computer or smartphone. They offer a more convenient way to access and manage your digital assets for everyday transactions and interactions with dApps. While they generally don’t offer the same level of offline security as hardware wallets, reputable non-custodial software wallets implement strong encryption and security measures to protect your private keys, which are typically stored on your device.
Exodus: Exodus is a highly popular and user-friendly desktop and mobile wallet known for its elegant interface and integrated exchange functionality powered by ShapeShift and Changelly. It supports a vast range of cryptocurrencies and allows for easy portfolio tracking. Exodus prioritizes user experience, making it an excellent choice for beginners and intermediate users. Its private keys are stored encrypted on your device, and users are prompted to back up their 12-word recovery phrase. Regular updates enhance security and add new features.
Trust Wallet: Acquired by Binance, Trust Wallet is a widely adopted mobile-first non-custodial wallet. It’s renowned for its extensive support for numerous blockchains and tokens, making it a versatile choice for users invested in various ecosystems. Trust Wallet allows users to stake certain cryptocurrencies directly from the app and provides seamless integration with dApps via its built-in browser. Like other software wallets, it generates a seed phrase for backup and stores private keys locally on your device.
MetaMask: MetaMask is arguably the most popular browser extension and mobile wallet for interacting with the Ethereum ecosystem and other EVM-compatible blockchains (e.g., Binance Smart Chain, Polygon). It’s indispensable for accessing decentralized applications (dApps), DeFi protocols, and NFTs. MetaMask allows users to manage multiple accounts and networks. Its security relies on a password and a 12-word seed phrase. While extremely convenient for dApp interaction, it’s crucial to be aware that leaving MetaMask logged in or downloading malicious extensions can pose security risks.
Atomic Wallet: Atomic Wallet is a desktop and mobile non-custodial wallet that emphasizes a clean interface and built-in exchange and staking features. It supports over 500 cryptocurrencies and offers a decentralized exchange (DEX) powered by Changelly. Atomic Wallet’s private keys are encrypted and stored on the user’s device, with a mandatory backup of the 12-word recovery phrase.
Key Advantages of Software Wallets:
- Convenience: Easy access for frequent transactions and dApp interaction.
- User-Friendly: Generally intuitive interfaces, suitable for beginners.
- Cost-Effective: Typically free to download and use.
- Mobile Integration: Many offer excellent mobile applications.
Disadvantages of Software Wallets:
- Online Vulnerability: Private keys are stored on internet-connected devices, making them susceptible to malware and hacking.
- Device Dependency: Loss or damage to the device can lead to fund loss if the seed phrase is not secured.
- Potential for Malware Infection: If the device is compromised, the wallet and its private keys can be at risk.
Multi-Signature Wallets: Enhancing Security Through Collaboration
Multi-signature (multisig) wallets add an extra layer of security by requiring multiple private keys to authorize a transaction. Instead of a single key, a multisig wallet is configured with a threshold, such as "2-of-3" or "3-of-5," meaning a specified number of signatures from a set of designated keys must be present for a transaction to be valid. This is particularly beneficial for businesses, organizations, or individuals who want to prevent a single point of failure or require collaborative control over funds.
While full multisig implementation can be more complex to set up and manage than single-signature wallets, services like Casa (though more of a platform leveraging multisig) and certain advanced wallet software offer solutions. For individual users, a common strategy is to use a hardware wallet for one key, a software wallet for another, and potentially store the third key securely offline. This significantly mitigates the risk of a single device compromise leading to complete fund loss.
Key Advantages of Multi-Signature Wallets:
- Enhanced Security: Prevents single points of failure and unauthorized access.
- Collaborative Control: Ideal for shared financial management.
- Redundancy: Loss of one key doesn’t necessarily mean loss of funds.
Disadvantages of Multi-Signature Wallets:
- Complexity: More challenging to set up and manage.
- Higher Transaction Fees (Potentially): Transactions involve multiple signatures, which can sometimes incur higher network fees.
- Need for Multiple Secure Key Storage: Requires diligent safeguarding of all involved private keys.
Choosing the Right Non-Custodial Wallet: Key Considerations
The "best" non-custodial wallet is subjective and depends heavily on individual needs, risk tolerance, and technical proficiency. Here are the critical factors to consider:
- Security Features: Prioritize wallets with robust encryption, secure element chips (for hardware wallets), and well-established security track records.
- Supported Assets: Ensure the wallet supports all the cryptocurrencies and tokens you intend to hold.
- User Interface (UI) and User Experience (UX): A user-friendly interface is crucial, especially for beginners, to avoid errors and ensure smooth operation.
- Backup and Recovery Options: Understand how to back up your seed phrase and the process for restoring your wallet.
- Reputation and Community Support: Look for wallets with positive reviews, active development, and a strong community that can offer assistance.
- Integration with dApps and Exchanges: If you plan to interact with DeFi or trade frequently, consider wallets with built-in dApp browsers or easy integration with exchanges.
- Cost: While most software wallets are free, hardware wallets involve an upfront investment.
Best Practices for Non-Custodial Wallet Security
Regardless of the wallet you choose, adhering to stringent security practices is paramount.
- Securely Store Your Seed Phrase: This cannot be overemphasized. Write it down physically, store it in multiple secure, offline locations, and never store it digitally (on your computer, phone, or cloud storage). Consider metal seed phrase backups for fire and water resistance.
- Use Strong, Unique Passwords: For software wallets and any associated accounts, employ strong, unique passwords and consider using a password manager.
- Enable Two-Factor Authentication (2FA): Where available for associated online accounts (e.g., exchange accounts used for funding your wallet), enable 2FA.
- Keep Your Software Updated: Regularly update your wallet software and operating system to patch security vulnerabilities.
- Beware of Phishing and Scams: Never share your seed phrase or private keys with anyone. Be cautious of suspicious links, emails, or unsolicited requests for information.
- Verify Transaction Details: Always double-check the recipient address and transaction amount before confirming any transaction.
- Consider a Hardware Wallet for Significant Holdings: For any substantial amount of crypto, a hardware wallet is a non-negotiable investment in security.
- Understand Your Risk: Non-custodial wallets offer control but also place the full responsibility for security on you. Educate yourself thoroughly.
The Future of Non-Custodial Wallets
The non-custodial wallet landscape is continuously evolving. We are seeing advancements in user experience, increased support for emerging blockchains, and innovative security features like multi-factor authentication for software wallets and enhanced social recovery mechanisms. The trend towards greater decentralization and user empowerment will undoubtedly continue, making the selection and secure management of non-custodial wallets an increasingly vital skill for anyone participating in the digital asset economy. By carefully evaluating the options and prioritizing robust security practices, individuals can confidently take control of their digital wealth.